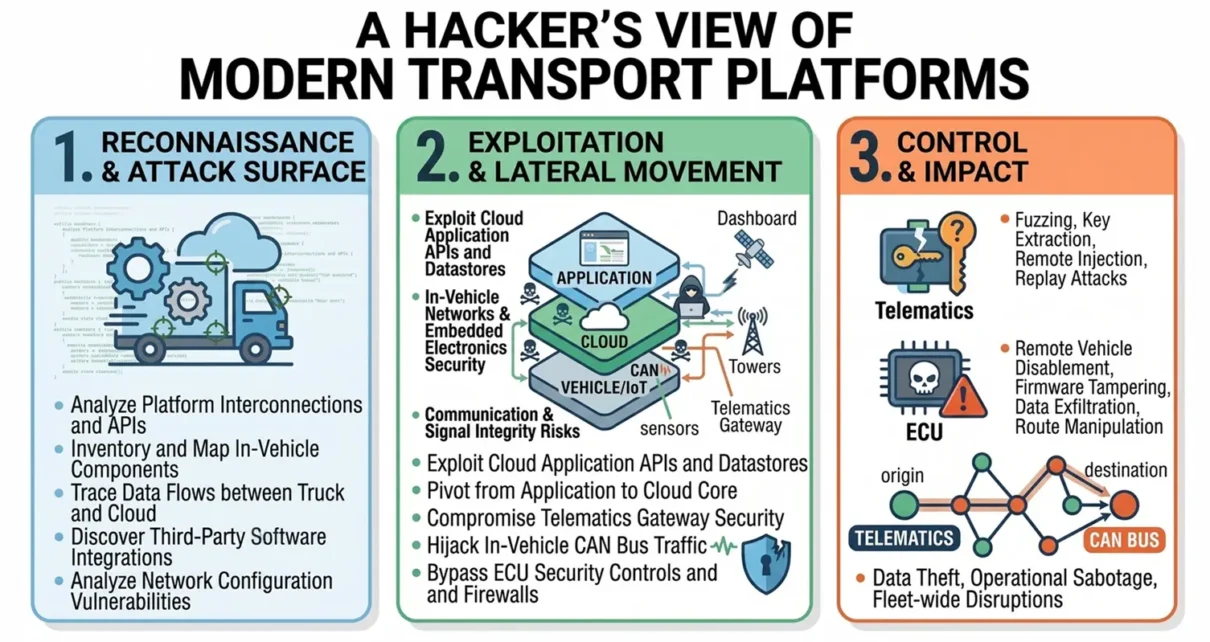
Modern transport platforms look simple from the outside. You book a shipment, track it, and wait for delivery. From a hacker’s perspective, though, these platforms are not just apps or services. They are layered electronic ecosystems made up of interconnected devices, networks, and embedded systems. Understanding how these systems work from the inside reveals both […]
Information Security
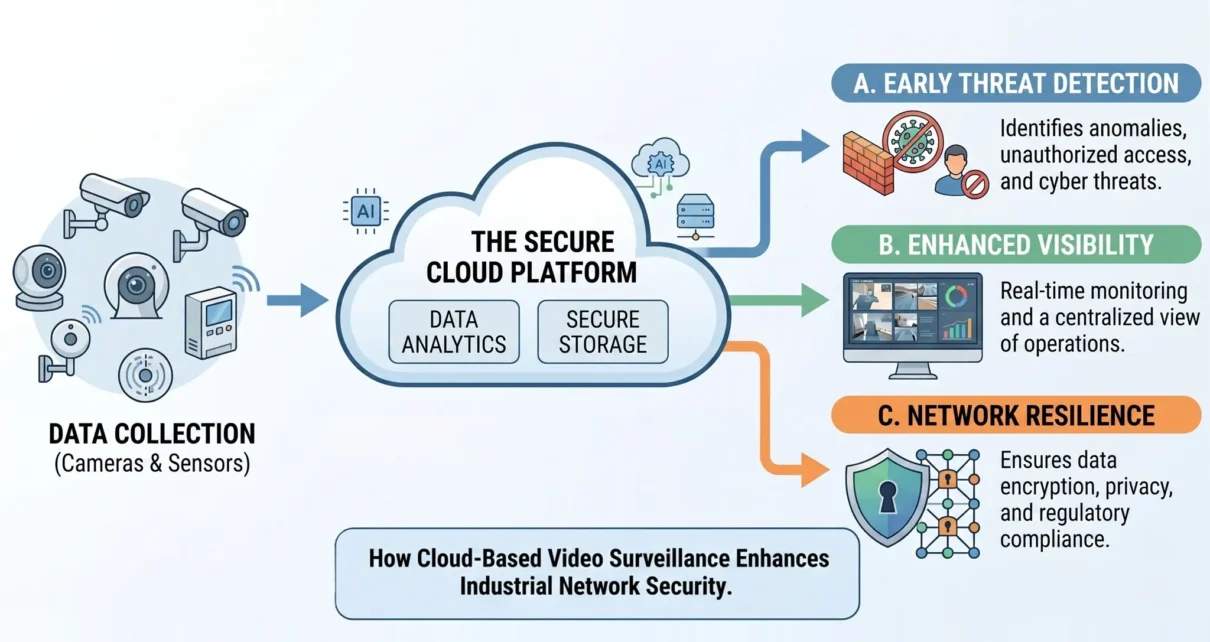
Cloud Video Surveillance for Industrial Network Security in Smart Factories
This article explores how cloud-based video surveillance enhances industrial network security and why it is essential for modern smart factories in 2026. The rapid evolution of smart manufacturing is redefining how industrial facilities approach both physical and cybersecurity. According to industry reports, the global video surveillance market is projected to grow from approximately USD 95 […]
11 Ways Industrial Firewalls Enhance Safety in Complex Factory Networks
Modern factories depend on interconnected systems that manage production, logistics, and quality control. As digital transformation reshapes industrial environments, network safety becomes one of the most critical factors in ensuring smooth operations. Cyber threats and system vulnerabilities pose significant risks to both productivity and worker safety, as well as regulatory compliance. Industrial firewalls play a […]
Advanced Access Control Systems for Business Security
This article explores how businesses can leverage advanced access control systems to elevate their security infrastructure effectively. As security threats grow more sophisticated, the demand for robust protection has never been higher. Businesses must prioritize safeguarding their assets, employees, and data. Access control systems have emerged as indispensable tools for strengthening security infrastructure. Beyond enhancing […]
Information Security Elements Confidentiality, Integrity & Availability
Hello Dear Friends, in this blog we will cover Information Security Elements in detail. Nowadays cyber (Computer Culture) crime where InfoTech is changing every second, we must prioritize the security of our digital information/assets over the security of our physical assets because we are living in an era when digital asset theft is significantly higher […]